Back up Virtual Machines
Portworx Backup now enables you to backup and restore KubeVirt Virtual Machines (VMs) running on Kubernetes clusters in an enterprise environment. Furthermore, this feature allows you to backup and restore VMs migrated from VMware environments and VMs running on OpenShift Virtualization. Portworx Backup detects these VMs to provide end to end data protection for VMs, VM disks, resource configuration, and network configuration data.
KubeVirt is Virtual Machine management add-on to provide a unified platform for VM workloads in the Kubernetes environment and allows VMs to run parallel with containers on Kubernetes, OpenShift, and other environments. With KubeVirt, you can run VM workloads and Kubernetes native workloads without requiring additional management tools or dedicated pipelines.
Prerequisites
Make sure that:
-
KubeVirt v1.0.0 or below and its dependent modules are installed on all managed Kubernetes clusters, source and destination clusters
-
qemu-guest-agentis installed on all the VMs to add KubeVirt specific pre-exec and post-exec rules -
Stork version 24.1.0 and above is installed on all application clusters
Following table lists out the the backup and restore workflows along with the scenarios supported by Portworx Backup as part of this feature:
| Resource types | Support |
|---|---|
| Clusters | Backup and restore on OCP, EKS, GKE, and Kubernetes Vanilla clusters |
| Backup locations | Backup and restore of VMs on S3 compliant object store and NFS backup locations |
| Cloud accounts | All the cloud accounts that Portworx Backup currently supports |
| Pre-exec and post-exec rules | Freeze/thaw (unfreeze) rules for crash consistent backups |
| Backup types | Manual and scheduled backups |
| Backups and restores |
Portworx Backup does not support 3-2-1 backup strategy for volumes with VolumeMode configured to block.
Backup and restore workflows supported by Portworx Backup for the VM resources is outlined in the following table:
| VM resources | Support |
|---|---|
| PVCs (CSI-based and non-CSI based) | Yes |
| Hotplug volumes | Yes (Supports hotplug volumes with persist enabled) |
| Kubernetes secrets (used as startup scripts, networkDataSecretRef) | Yes (Manual selection of these resources are required during creation of backup) |
| NetworkAttachmentDefinition | Yes |
| Network Policy | No |
| Service object | |
| Data volumes (DV) | No (Supports backup and restores of PVCs associated with data volumes only) |
| Data volume template (serves as a template to create data volume for a VM) | No (Supports backup and restores of PVCs associated with data volume templates only) |
| Yes | |
| No |
-
Portworx Backup does not support backup and restore of VM instances configured with multiple network interfaces and VMs created with virtualMachineInstance without VirtualMachine object.
-
Portworx Backup creates a backup of VM resources with auto selection of all the resources with few exceptions outlined in the table above. Dependent VirtualMachine resources that are not part of VirtualMachine configuration will not be auto selected. For example, Network Policy, Service, and so on.
-
If you intend to use CLI, you can use the existing namespace based backup approach by adding freeze/thaw rules explicitly as pre/post exec rules.
To back up and restore your KubeVirt VMs (or namespaces that contains your VMs):
-
Login to Portworx Backup web console.
-
From the home page, add a cloud account.
-
Configure a backup location.
-
Add the required type of cluster.
-
Create pre-exec and post-exec backup rules or use built-in (or default rules) available in Portworx Backup. To create pre-exec and post-exec backup rules for file-system backups, refer Backup Rules for file-system consistent backups.
-
Create a VM backup.
Portworx Backup creates backups of VMs regardless of its state. The VMs restored from backup always come back to running state, even if the VM was stopped during the backup creation process.
Create a VM backup
To create a backup of your VM:
-
Login to Portworx Backup web console.
-
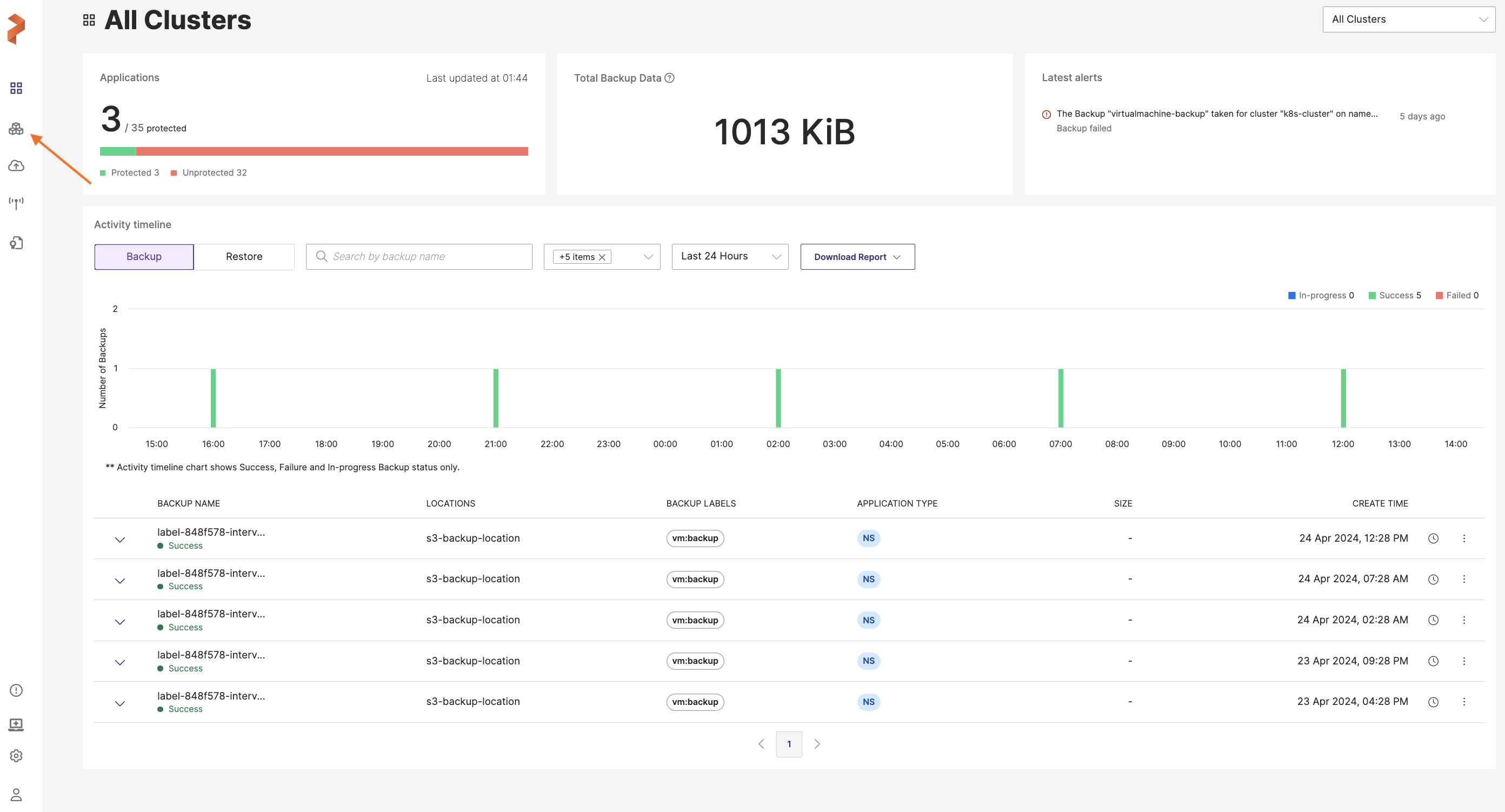
From the home page, click on the Clusters icon from the left navigation pane.
-
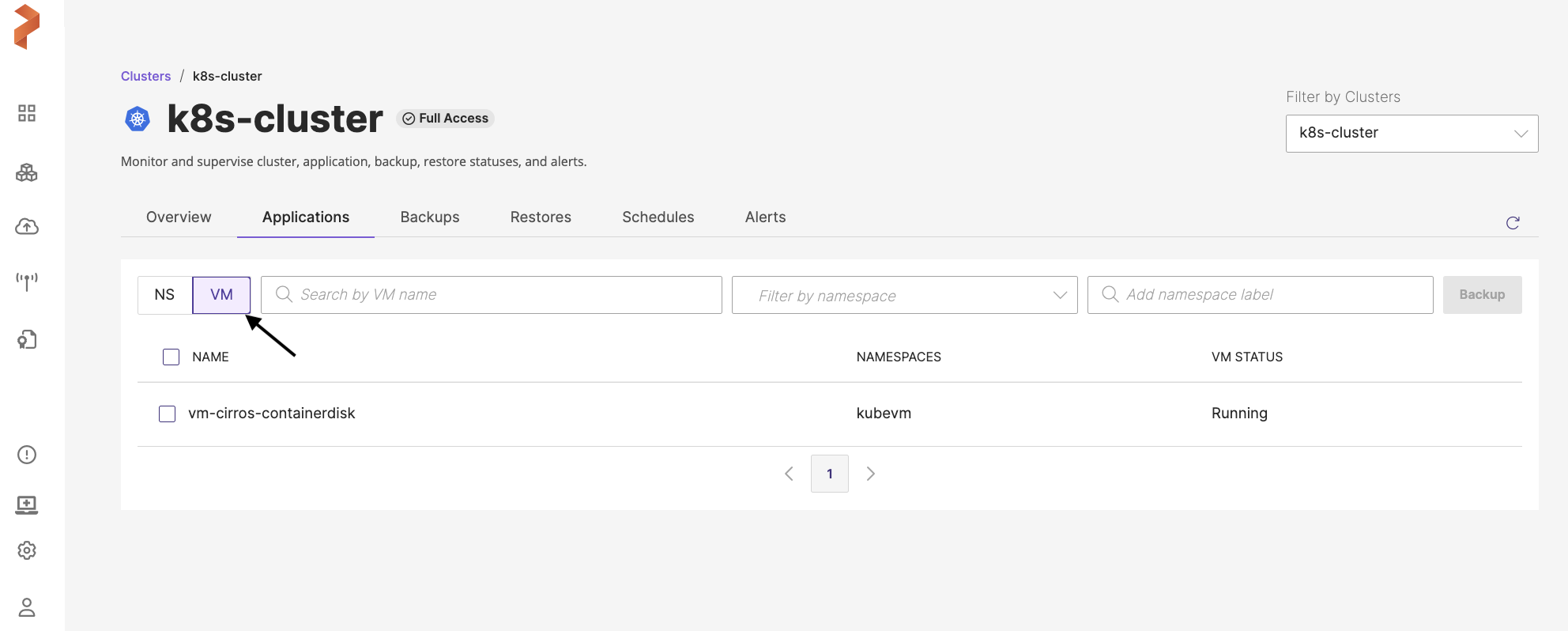
Click on the application cluster that contains the VM to be backed up.
Portworx Backup does not allow individual selection of VM resources for your backup. You need to select the entire VM to create a backup. All the resources in the VM will be backed up.
-
Click on the Applications tab and then go to the VM tab.
-
Select the VM(s) to be backed up and then click Backup.
-
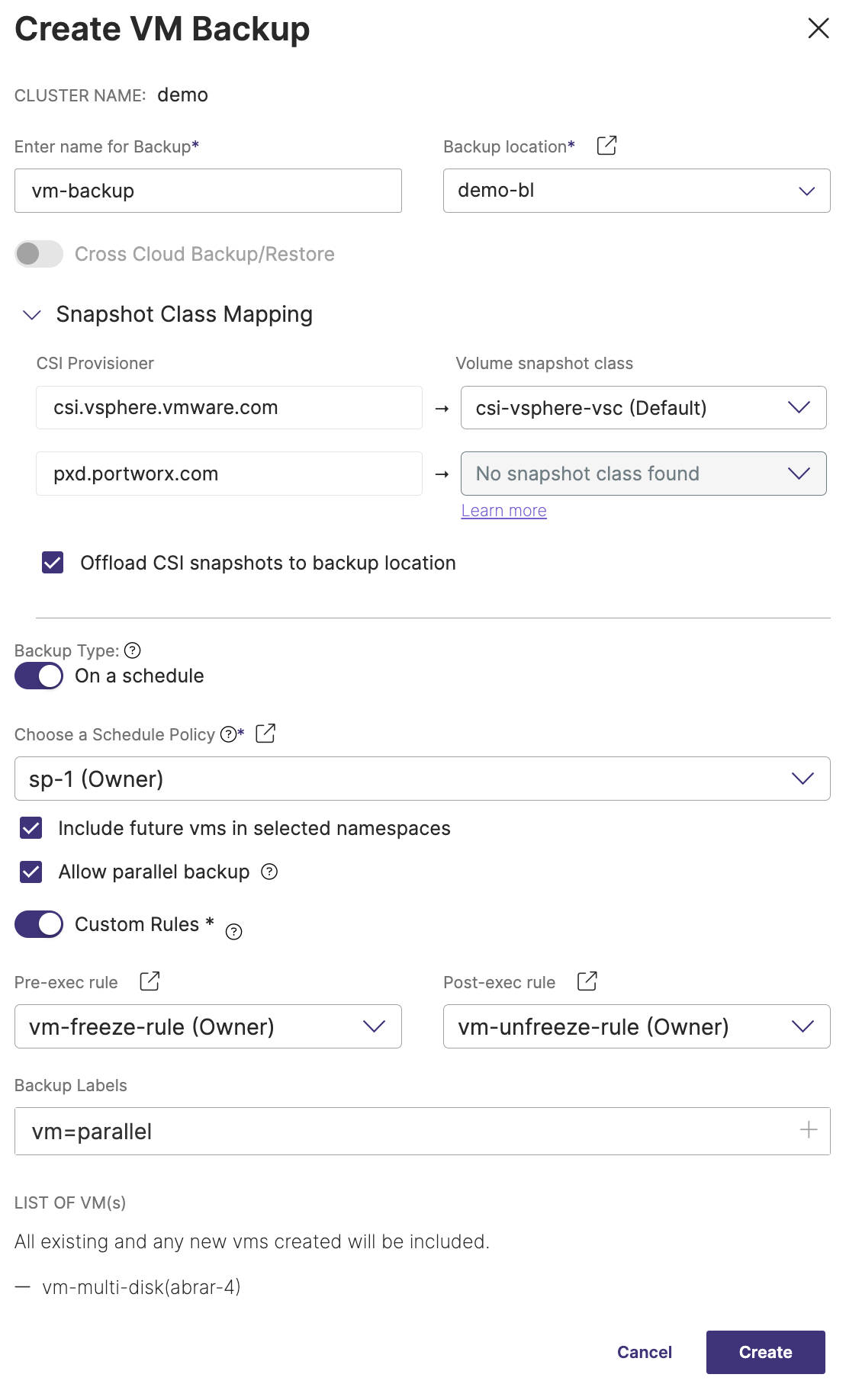
In the Create Backup window, populate the following values:
For more information on these fields, refer to Create manual backup and Create scheduled backup topics.
-
Enter name for Backup: the name of the backup you want to be displayed in the Portworx Backup web console
-
Backup location: the S3 bucket or NFS backup location you want to store your backups onto
-
Cross-cloud Backup/Restore: this toggle button is disabled by default for VM backups, because Portworx Backup currently does not support cross-cloud (with KDMP driver) backups and restores for VM-based backups.
-
Snapshot Class Mapping: this option is always enabled for VM backups and allows you to map the snapshot class for your backup. You can map a snapshot class only for non-Portworx provisioners (CSI provisioners).
- Offload CSI snapshots to backup location: offloads snapshots to any S3-based or NFS backup location
-
Backup Type: manual or scheduled
- Disable: creates a backup immediately, it is manual way of creating backups
- Enable: automates the creation of backup process and creates the backup at the scheduled time
-
Choose a Schedule Policy: when you select all VMs of the cluster to take a backup and choose a schedule policy, you will see the following options:
- Include future vms in selected namespaces: adds the future VMs that will be created or added in future for the selected namespaces of the scheduled backup
- Allow parallel backup: select this option to enable PXB to trigger a new scheduled backup even when the previous scheduled backup is still in progress (uploading snapshots to the cloud). Refer to Parallel backup schedules for more information.
-
Custom Rules
-
Disable: Portworx Backup runs default or built-in freeze/thaw rule, does not require the user to create rules manually
-
Enable: allows you to select the custom (user-defined) pre-exec and post-exec rule (freeze/thaw rule). If you enable and do not select any rules, Portworx Backup creates backup without applying any rule.
-
Pre-exec rule: choose the custom pre-exec rule from the drop-down
-
Post-exec rule: choose the custom post-exec rule from the drop-down
-
-
Backup Labels: apply the label(s) in key=value or key:value format to your backup to filter the required backups when needed at a later point in time
-
LIST OF VM(s): lists out the selected VMs and creates a backup
Portworx Backup creates a backup of your entire VM. To view the backup you just created, navigate to the Backups > VM tab from your application cluster page.